|
|
|
|
Checking your favorite software supplier or doing a quick Google search will identify many software tools for trashed file recovery will allow anyone to restore that data. You can even read the reviews on both how well they work and their ease of use. Why-Who Needs It? Oh you accidentally trashed that term paper or the draft of your new book you were working against the clock to complete. Your backups our out of date, so where do you turn? Hard disk recovery tools of course. The same tool gave the capability to bulletproof your drive that even a supper computer will have trouble getting at your data.
Caveat: this works only if the data has not been over-written. This statement, as youll se later is not completely true, but is valid if you overwrite all the data many times. But then you system is also dead and gone. Is there a middle ground — read on!
Reformatting the hard drive is a bit more secure than simply erasing the files. Formatting a disk does not erase the data on the disk, only the address tables. It makes it much more difficult to recover the files. However a computer specialist would be able to recover most or all the data that was on the disk before the reformat.
For those who accidentally reformat a hard disk, being able to recover most or all the data that was on the disk is a good thing. However, if youre preparing a system for retirement to a charity or other organization, this obviously makes you more vulnerable to data theft.
For some individual users and businesses, a disk format may be something you consider secure enough depending, of course, on the type of data and information you saved to your computer. As long as people understand that formatting is not a 100 percent secure way to completely remove all data from your computer, then they are able to make the choice between formatting and even more secure methods. If you have decided a disk format is a good choice, at the very least you should do a full format rather than a quick format.
Disk Wiping Options (aka a Data Dump)
Disk wiping is an even more secure process than reformatting. The term disk wiping is not only used in reference to hard drives but any storage device such as CDs, RAIDs, thumb drives, and others. Disk wiping is a secure method of ensuring that data, including company and individually licensed software on your computer and storage devices, is irrecoverably deleted before recycling or donating the equipment.
Because previously stored data can be brought back with the right software and applications, the disk wiping process will actually overwrite your entire hard drive several times with data. Once you wipe your disk, you will find it all but impossible to retrieve the data that was on the drive before doing so.
While disk-wiping algorithms differ from product to product, they all will generally write the entire disk with a number (zero or one), then reformat the disk. The more times the disk is overwritten and formatted, the more secure the disk wipe is, but the trade-off is the extra time to perform additional rewrites. Disk wipe applications will typically overwrite the master boot record, partition table, and every sector of the hard drive.
The government standard (DoD 5220.22-M), considered a medium security level, specifies three full iterations to completely overwrite a hard drive. Each iteration makes two write-passes over the entire drive; the first pass inscribes ones (1) over the drive surface and the second inscribes zeros (0) onto the surface. After the third iteration, a government-designated code of 246 is written across the drive, and then it is verified by a final pass that uses a read-verify process.
There are a variety of products available for different operating systems that you can purchase or freely downloaded online to perform more secure disk wipes. If time to perform the disk wipe is a consideration, there are also tech security companies who offer disk wipe services.
Did You Know? In 2003 two MIT students purchased 158 used disk drives from various locations and found more than 5,000 credit card numbers, medical reports, detailed personal and corporate financial information, and several gigabytes worth of personal email and pornography on those drives.
The only product I know enough to share is Drive Genius. My pre OS X favorite a Norton Product was discontinued. Requirements: Mac OS X 10.2 or higher. Shareware $99 Drive Genius is an OS X utility designed to provide storage management. Featuring an easy-to-use interface, Drive Genius is packed with powerful tools such as a drive optimizer, a comprehensive repair facility for analyzing, repairing and rebuilding volumes, plus excellent testing capabilities with media surface scanning, performance benchmarking and data integrity checking. It can be used to initialize drives, create and delete partitions, and erases them securely as per Department of Defenses standard.
Hard Drive Erasing
To erase a Macintosh hard drive, boot with a Mac OS X install CD and use the Disk Utility on the drive. Apple Tech Note 107437 gives this procedure for Mac OS X Systems:
Note: This refers to a full Mac OS X 10.4.9 or later CD included with a computer, not to the update-only 10.2.3 CD. However the software is available to work with older OX X systems from Prosoft Engineering, its developer.
Steps for Zeroing Data Using Apples Disk Utility Software
Note to erase your boot volume you must mount the Disk Utility containing disk, since the software can not erase its on operating system. These steps assume you have a Mac OS X 10.2.3 or later CD:
For a more secure method of erasing of data, you can select the checkbox 8 Way Random Write Format instead of or in addition to selecting Zero all data. This process could take several hours.
For those wanting to Clean individual files, note this section from Apples technical note: Secure Empty Trash You can securely empty the Trash in Mac OS X. While in the Finder, from the File menu choose Secure Empty Trash.
Note: When you securely empty the Trash, the deleted data cannot be recovered by disk utilities. You should only do this if you have a backup or you are sure you will never need the data again.
For machines which boot only Mac OS 9 or less, use Drive Setup, Apple HD SC Setup, or Internal HD Format, and select the option to zero out and/or low level format the disk. These programs are usually in the Utilities Folder on the install CDs for the various versions of the Mac OS. Apple Tech Note 21103 has more information.
A Shareware Option — ShredIt is cross-platform: it is an ideal choice for the multi-platform office. There is a ShredIt version for Mac OS X, Mac OS 9, Mac OS 8, Mac OS 7, Windows 95, Windows 98, Windows NT, Windows 2000, Windows ME, and Windows XP. You can wipe a file or erase a hard drive with this easy-to-use File Shredder — computer privacy software that shreds data so it cant be recovered. Its available on a CD-ROM for $34.95 or $25.95 for the download. Users who need to dispose of confidential data on an ongoing basis appreciate how easy ShredIt is to use. Just drag the file on to the ShredIt icon and ShredIt File Shredder will wipe the file data so it cant be recovered. If your not sure you need a shredding tool check out Do you need a File Shredder? Take the ShredIt Data Shredder Test. It takes less than 2 minutes, to find out.
Ive tested the software in trial mode, and it appears to be a fine product, but full testing will wait my having more time. Of importance to me is that ShredIt shreds everything. It will erase a file, folders, disk free space, files youve already deleted, whole hard drives, external hard drives, thumb flash drives and even a floppy or a Zip disk. Now I do the later medium with an old tape degausser, left over from my reel-to-reel days.
Remember: Throwing data in the computer trash does not remove the file contents from the hard drive; the data can be recovered by someone else. Users who want to erase a hard drive before disposing of a an old computer can be confident that using ShredIt Hard Drive Cleaner will erase the hard drive so the data cannot be recovered by the next owner.
In Part from Apple Barrel, Ridgecrest, CA Harry Babad, macCompanion From Paul Taylors Hints and Tips Newsletter – October 2007 PS
I cant let a thought flyaway undocumented, so back to restore simply trashed data. Check your favorite software supplier or do a quick Google or MacUser search to identify many of software tools for trashed file recovery will allow anyone to restore that data. Do read the review carefully because a bad tool can do more damage that you should bargain for. Focus on both how well they work and their ease of use. Check blogs to see what havoc they a product might have caused — remember the software vendor is not liable to Caveat emptor.
Oh, you accidentally trashed that term paper or the draft of your new book you were working against the clock to complete. Your backups our out of date, so where do you turn? Hard disk recovery tools of course. The same tool gave the capability to bulletproof your drive that even a supper computer will have trouble getting at your data. Examples of available product include Data Rescue II and low-rated Disk Doctors Mac Data Recovery 1.0. Theres one Id not heard of before [Macintosh Data Recovery which seem to be associated with a data recovery service. Despite the seemingly similar titles, they seem to be different products.
PPS
Next month: eMail Etiquette — based on what fills my inbox, no not spam, you have not heard it all yet! |

 Safe, Secure and Polite Macin — Things You Should Practice
Safe, Secure and Polite Macin — Things You Should Practice They Say Charity Begins
at Home — However, if youve decided to donate your old computer to a
charity, local group or school, its important to make sure your computers hard
drive is completely free of data.
They Say Charity Begins
at Home — However, if youve decided to donate your old computer to a
charity, local group or school, its important to make sure your computers hard
drive is completely free of data. Hard
Drive — A hard disk
drive (HDD), commonly referred to, as a hard
drive, hard disk, or fixed disk drive, is a non-volatile storage device, which
stores digitally encoded data on rapidly rotating platters with magnetic
surfaces (e.g., its platter). Strictly speaking, "drive" refers to a
device distinct from its medium, such as a tape drive and its tape, or a floppy
disk drive and its floppy disk.
Hard
Drive — A hard disk
drive (HDD), commonly referred to, as a hard
drive, hard disk, or fixed disk drive, is a non-volatile storage device, which
stores digitally encoded data on rapidly rotating platters with magnetic
surfaces (e.g., its platter). Strictly speaking, "drive" refers to a
device distinct from its medium, such as a tape drive and its tape, or a floppy
disk drive and its floppy disk.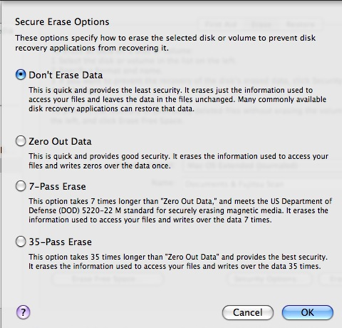
 Drive Genius 2.1.x
Drive Genius 2.1.x Why - Who Needs It?
Why - Who Needs It?